Setting up access management and permissions
5.1 Access Management records
View all the identification records on the device, which can be grouped and filtered by device. The data body temperature value is greater than or equal to 37.3 degrees to display red font, less than 37.3 degrees to display green font, no temperature data display "none". There are three Accessage states: normal body temperature, abnormal body temperature and no mask.
5.1.1 Export
5.1.2 Export records
The system
will record the operation of each export Access record and generate an export
record. If the export succeeds, the export status will be recorded as
"completed", and if the export is canceled, the export status will be
recorded as "canceled". The export record in the completed state
allows downloading the exported excel file again, and all export records are
allowed to be deleted.
5.2.1 Employee Access permission settings
Steps: Enter the [Access permission] page and click the "Employee Access Authorization" button.
Access permission
1) Select personnel, devices, Access permission and permanent effective time, and click "Save" button to start Access permission. After the device is successfully authorized, the person can Access the gate and the validity period is permanent.
2) Select personnel, devices, Access permission and temporary effective time, and click "Save" button to start Access permission. After the device is successfully authorized, the person can Access through the gate within the time range set by the validity period. If the validity period is exceeded, the recognition fails.
Description of Access permission:
· Click the Save button to start the Access permission. Present the current synchronization status, authorization progress, number of successes and failures of each device in the form of a list, and display device names.
· The person who failed the authorization is recorded in the "Verification Failure Description" table. You can click "Export Settings Failed Number" to export and view the authorization failure information.
· The person who fails the authorization, after modifying the corresponding failure information, can re-authorize until the authorization is successful.
Revoke Access permission
Select a person, select a device, de-authorize, and click the "Save" button to start revoking the permission. The de-authorization is the same as the "Access permission" logic, except that the selected person is removed from the selected device.
5.2.2 Visitor Access permission settings
Steps: On the [Access permission] page, click the "Visitor Access permission" button.
Access permission
Select the visitor, select the device, Access permission and valid time range, and click the "Save" button to start the Access permission. After successful authorization on the device side, the visitor can Access the gate to be valid within the set effective time range.
Description of Access permission:
· Click the Save button to start the Access permission. Present the current synchronization status of each device in the form of a list, showing the device name, synchronization Access permission, number of successful and failed. The person who failed the permission is recorded in the "Verification Failure Description" table. You can click "Export Settings Failed Number" to export and view the permission failure information.
Visitors who have failed authorization can revise the authorization after revising· the corresponding failure information until the authorization is successful.
Revoke Access permission
Select personnel and equipment and revoke the permission. Click the "Save" button to start. Revoke permission is the same as "Access permission", except that the reassigned personnel are removed from the original equipment.
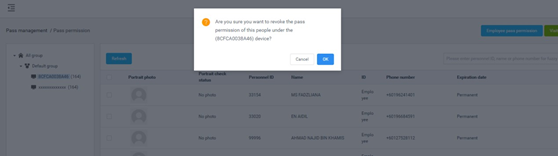
5.2.3 Revoke permission
In the authorized personnel list, you can click the
"Revoke permission" button behind the list record to release the
authorization. After the removal is successful, the corresponding employees and
visitors will have no Access permissions. You can also check personnel records
and click "Remove permissions" for batch operations.
5.2.4 Refresh permission information
On the [Access permission] page, click the "Refresh" button to refresh all authorized information in the list to the latest state.
5.3 Blacklist monitoring
5.3.1 Blacklist monitoring settings
Steps: Enter the [Blacklist monitoring] page and click the
"Blacklist monitoring settings" button.
Blacklist monitoring settings
1.
Select the blacklist and device and snap to report. Click the "Save" button to start the blacklist monitoring. After the device is successfully monitored,
the person will be recognized and captured when reporting through the gate.
Select the blacklist and device, choose to enable the
snapshot report function, and enable
Description of Access permission:
1. Click the Sure to start the blacklist monitoring. Present the current synchronization status of each device in the form of a list, display the device name, synchronization monitoring progress, the number of successful and the number of failed. The monitoring failures are recorded in the "Export Blacklist Monitoring Failure Information" table. You can click the export table to view the monitoring failure information.
2. Blacklist personnel who failed to monitor, after modifying the corresponding failure information, can re-monitor the settings until the monitoring registration is successful.
Revoke blacklist monitoring
Select blacklist and device, and release blacklist monitoring. Click the "Save" button to start the release.
Enter the [Blacklist monitoring] page, click the "Identify Record Inquiry" button to enter the [Identify record inquiry] page, and display the identification records of all blacklist personnel. Blacklist identification records can be selected according to grouping, device, and date range inquiries.
5.3.3 Remove monitoring
In the
blacklist monitoring personnel list, you can click the "remove
monitoring" button behind the list record to release monitoring. After the
removal is successful, the blacklist removes the snapshot monitoring or alarm
from the selected device. You can also check the personnel record and click
"remove monitoring" to perform batch operations.
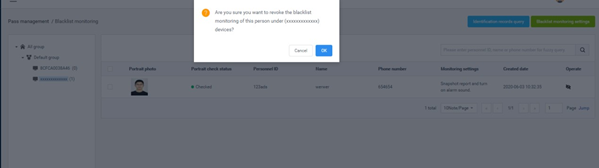
In the blacklist monitoring personnel list, you can click the "remove monitoring" button behind the list record to release monitoring. After the removal is successful, the blacklist removes the snapshot monitoring or alarm from the selected device. You can also check the personnel record and click "remove monitoring" to perform batch operations.
5.4 Permission records
Permission details are as follow:
Related Articles
Using the system management options.
6.1 Group structure [Group structure] The module is used to manage the group structure and enterprise user information management in the enterprise. The hierarchical relationship is created and managed by admin or enterprise administrator ...Using attendance management
7.0 Attendance rules [Attendance rules] Add, modify and delete related rules including shifts, holidays, public holidays, and device groups, etc. are set in this module. 7.1.1 Shift settings The shift setting contains a ...How to install the central management software
Please download the setup file from here. File name: SMART_PASS_steup_V2.5.0.2.exe Please allow access/ provide permissions to install the software in Windows PC/ Server. Please note: this software will not work in Mac OS. Please ensure you have ...Setting up new employee and personnel information
4.1 Employee list The employee list is used to manage employee information, such as viewing, adding, editing, and exporting employee information. Employee information can be added individually or in bulk. The batch adding operation requires ...Using the console or central management software
Console It provides an overview of the number of devices and online status; statistics on the face scan (total face scan, employee face scan, visitor face scan, stranger's face scan); today's Access and real-time monitoring (employees, visitors, ...